
Mapping EUCC to Common Criteria: A Technical Overview of Assurance Levels and Evaluation Requirements
The EU Cybersecurity Certification Scheme on Common Criteria (EUCC) is now the operative framework for ICT product security certification in Europe. Established by Commission Implementing Regulation (EU) 2024/482 on 31 January 2024 and fully applicable from 27 February 2025, the EUCC replaces the fragmented SOG-IS national certification landscape with a single, harmonized scheme built on ISO/IEC 15408, the international Common Criteria standard. If your product currently holds or is pursuing a Common Criteria certificate, the EUCC changes what assurance actually means, how evaluators assess vulnerability, and what evidence you need to provide.
This article maps the technical architecture of EUCC against classic Common Criteria: assurance levels, vulnerability analysis requirements, evaluation depth, and the evidence your team must deliver before a certification body issues a certificate.
Common Criteria and EUCC: The same foundation, a different framework
Common Criteria (CC) is an international standard under ISO/IEC 15408 that provides a structured methodology for evaluating the security properties of IT products. It defines Security Functional Requirements (SFRs), specifying what a product is required to do, and Security Assurance Requirements (SARs), defining how thoroughly the evaluation must verify those functions. The result is a certificate tied to a specific Security Target (ST), which describes the product's evaluated configuration, threat model, and security objectives.
The EUCC does not replace this methodology. Instead, it governs who certifies, at what depth, and under which national oversight structure within the EU. Every EUCC evaluation still uses the CC standard (ISO/IEC 15408), the Common Evaluation Methodology (CEM), and applicable state-of-the-art documents. What EUCC adds is an EU-level governance model under ENISA's supervision, replacing independent national schemes with a unified conformity assessment framework. This governance shift did not happen in isolation. The EUCC was designed as part of a broader EU regulatory architecture, where a harmonized certification scheme creates a direct bridge to product-level compliance obligations under horizontal legislation. As we explored in Cyber Resilience Act & EUCC Explained: Key Differences, Overlaps and Compliance Pathways, this alignment is key for long-term market access under the Cyber Resilience Act (CRA). Products certified at EUCC Substantial or High level qualify for a presumption of conformity with the CRA's essential cybersecurity requirements.
EAL Levels vs. EUCC Assurance Levels: What changed
Classic Common Criteria uses seven Evaluation Assurance Levels (EAL1–EAL7) to grade the depth of an evaluation. Higher EAL numbers mean more rigorous scrutiny of design documentation, testing procedures, and development environment controls.
The EUCC does not retire EAL levels, but it repositions them under two broader assurance categories defined by the EU Cybersecurity Act (CSA): Substantial and High. Crucially, the EUCC shifts the primary classification criterion from EAL number to Vulnerability Analysis (AVA_VAN) level. EALs are still visible on EUCC certificates where applicable, but the AVA_VAN level is always stated and drives the conformity assessment path.
Substantial Assurance (EAL1–EAL3 / AVA_VAN.1–AVA_VAN.2)
Substantial assurance covers the lower end of the CC spectrum. Products at this level must demonstrate that publicly known vulnerabilities are absent and that security functionalities are correctly implemented. The evaluation targets threats from actors with limited skills and resources.
AVA_VAN.1 conducts a basic analysis to identify obvious security flaws. AVA_VAN.2 adds structured independent testing to verify resistance to low-skill attacks. Self-assessment is not permitted; all evaluations require a Conformity Assessment Body (CAB). At this level, CABs may issue certificates without mandatory national scheme review, subject to their accreditation scope.
High Assurance (EAL4–EAL7 / AVA_VAN.3–AVA_VAN.5)
High assurance covers the demanding upper tier. Products evaluated here face attacks from skilled, well-resourced adversaries. The evaluation must include structured penetration testing, independent vulnerability analysis, and formal verification methods at the top sub-levels.
AVA_VAN.3 involves systematic, independent vulnerability analysis against methodical attackers. AVA_VAN.4 and AVA_VAN.5 require advanced penetration techniques and, where applicable, formal security models. All High assurance certifications require national cybersecurity certification authority (NCCA) review. Certification above AVA_VAN.3 is generally only possible within a defined Technical Domain or against a certified, state-of-the-art Protection Profile.
For a deeper breakdown of how these levels map to product risk categories, see our overview: Common Criteria Assurance Levels: An Overview of the Evaluation Criteria and Methodology.

Security assurance requirements: What Evaluators actually examine
Under both classic CC and EUCC, an evaluation is built around Security Assurance Requirements (SARs). These define the evidence and testing activities needed to confirm the product's security posture. The relevant SAR families map directly to the assurance level:
ASE (Security Target): The foundational document for the entire evaluation. The Security Target defines the product's evaluated scope, security objectives, threat model, and the specific SFRs and SARs the product is being assessed against. All other evaluation classes build on what is stated here.
ADV (Development): Architecture information, functional specification, and implementation representation. At higher EALs, this extends to full source code review and formal security policy models.
AGD (Guidance Documents): Operational user guidance and preparative procedures. Evaluators confirm that guides accurately describe the secure configuration and operation of the evaluated product.
ALC (Life Cycle Support): Development security, CM automation, flaw remediation, and tools and techniques. EUCC places explicit emphasis on ongoing patch management obligations, requiring certificate holders to maintain active vulnerability management processes throughout the certificate lifecycle.
ATE (Tests): Developer test coverage, independent functional testing, and at higher assurance levels, penetration testing using attack potential calculations.
AVA_VAN (Vulnerability Analysis): The central differentiator under EUCC. This class determines which assurance level the product attains. Evaluators analyze the TOE for exploitable vulnerabilities using attack potential methodology, rating the effort, knowledge, and resources an attacker would need to exploit a given flaw.
The EUCC implementing regulation (EU) 2024/482 mandates that all evaluation activities adhere to the CC standard, the CEM, and applicable state-of-the-art documents listed in Annex I. Applicants must provide comprehensive documentation, including previous evaluation results where applicable.
For a practical reference on preparing each of these document classes for evaluation, download the Guide and Checklist for Common Criteria Evaluations, updated for the EUCC scheme.
Attack Potential and Vulnerability Analysis: The core technical difference
Classic Common Criteria tied assurance depth primarily to EAL number, where higher levels meant more documentation and process rigor. EUCC shifts the primary criterion to AVA_VAN level, anchoring certification directly to vulnerability analysis and real-world attack resistance rather than documentation compliance alone. Evaluators must explicitly calculate attack potential for every identified vulnerability. Attack potential is calculated based on five factors: elapsed time, specialist expertise, knowledge of the TOE, window of opportunity, and IT hardware/software or other equipment. The resulting score determines whether an identified vulnerability is exploitable by a Basic, Enhanced-Basic, Moderate, High, or Beyond-High attack, and therefore whether it represents a finding that affects certification status. This methodology means that EUCC certifications are not static. If a vulnerability is discovered post-certification that affects the attack potential rating, the certificate holder must produce a vulnerability impact analysis report and notify the certification body. Depending on severity, the certificate may be suspended or revoked. For technical teams working at High assurance, the key planning constraint is that AVA_VAN.4 and AVA_VAN.5 require Technical Domain coverage or a certified Protection Profile. Currently, Technical Domains cover smartcards and hardware devices with security boxes. Applying for High assurance outside these domains requires a state-of-the-art Protection Profile endorsed under EUCC Annex I.
Conformity Assessment: How EUCC evaluation is structured
The EUCC certification process follows this structure:
Step 1: Application and Scope Definition. The applicant defines the Target of Evaluation (TOE), selects the AVA_VAN level, and prepares the Security Target. Protection Profile alignment is verified where applicable.
Step 2: Evaluation by CAB. The CAB performs evidence review, independent testing, and vulnerability analysis. The evaluation is documented in an Evaluation Technical Report (ETR).
Step 3: Certification. For Substantial level, the CAB issues the certificate directly (subject to accreditation). For High level, the national NCCA reviews the ETR before a certificate is issued.
Step 4: Post-Certification Maintenance. The certificate holder must maintain a vulnerability management process, report newly discovered vulnerabilities as required under Articles 32-39 of Commission Implementing Regulation (EU) 2024/482, and apply for re-assessment if changes to the certified product affect the security claims.
EUCC certificates are valid for up to five years, with mandatory updates when product changes affect evaluated security. This lifecycle obligation is a significant operational requirement compared to the one-time model of some earlier CC certifications.
For what this means specifically at the High assurance tier, see Implementing EUCC: What High-Assurance Certification Requires Beyond Traditional Common Criteria Approaches.
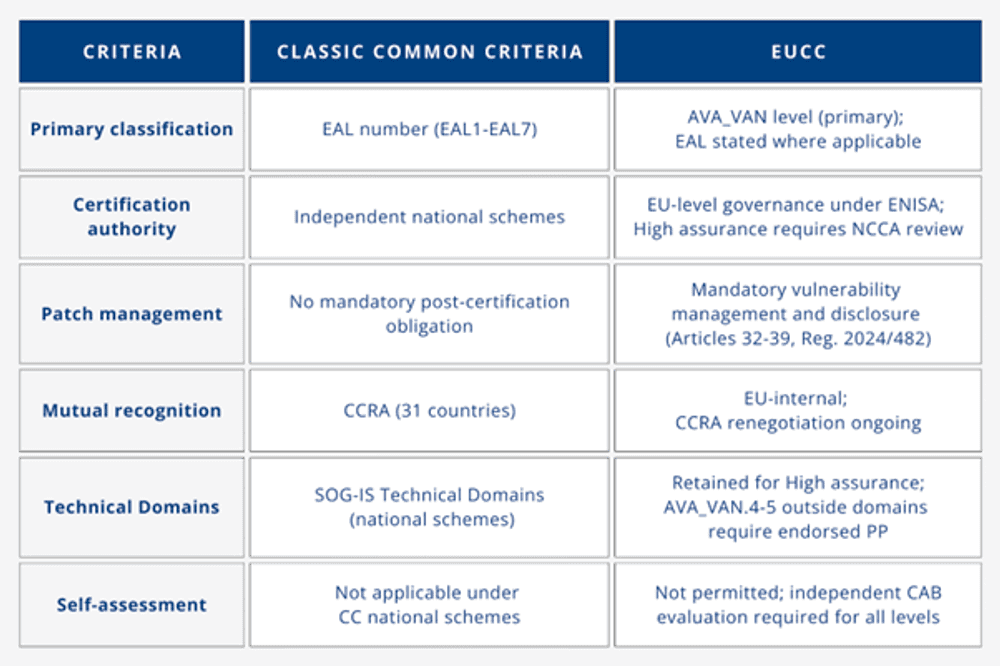
EUCC vs. Classic Common Criteria: Key differences at a glance
(Primary classification criterion: CC uses EAL number; EUCC uses AVA_VAN level. EAL is still stated on certificates where applicable, but it is secondary.
Certification authority: CC certifications are issued by national schemes independently. EUCC operates under EU-level governance with ENISA oversight; High assurance requires NCCA review.
Patch management: Traditional CC had no mandatory post-certification obligation. EUCC introduces explicit vulnerability management and disclosure requirements under Articles 32-39 of the implementing regulation, requiring continuous monitoring and reporting.
Mutual recognition: CC operates under the CCRA (31 countries). EUCC is EU-internal; CCRA renegotiation is ongoing to achieve alignment with the new scheme.
Technical Domains: EUCC retains SOG-IS Technical Domains for High assurance. Evaluations above AVA_VAN.3 outside these domains require an endorsed PP.
Self-assessment: Not permitted under EUCC. All certifications require independent CAB evaluation.)
Practical implications for product teams
If your product is targeting EU market entry with security certification, the EUCC path is clear. Define your threat model early. The AVA_VAN level you need determines the entire scope of evaluation, documentation, and testing. Over-engineering to AVA_VAN.5 when your threat profile supports AVA_VAN.2 creates cost and timeline risk without certification benefit.
Start with a Security Target that accurately bounds the TOE. Mismatched scope between the ST and actual product is the most common source of evaluation delays.
For high-assurance products in Technical Domains (smartcards, hardware security modules), align to the applicable Protection Profile early. Deviating from the PP scope without documented justification will be flagged during evaluation.
Plan for lifecycle obligations from day one. Post-certification vulnerability management is not optional. Build the internal process before you apply, not after you receive the certificate.
Download EUCC Study 2026 for a comprehensive walkthrough of certification steps, timelines, and evidence requirements under the current scheme. For a step-by-step guide to the full application and evaluation process, see How to Prepare and Apply for EUCC Certification for Your Product.
Start Your EUCC Evaluation with QIMA CCLab
Whether you are mapping an existing CC certification to EUCC, planning a first evaluation, or preparing developer documentation, QIMA CCLab's technical team works directly with your engineering and compliance functions to keep the evaluation on scope and on schedule.
FAQ
How does the EUCC differ from previous certification schemes?
The EUCC is designed to replace the previous SOG-IS Mutual Recognition Agreement (MRA) and introduces a unified framework under the EU Cybersecurity Act (CSA). This new scheme standardizes the certification process across EU member states, reducing complexity and fostering mutual recognition of certified products.
What are the benefits of obtaining EUCC certification for my product?
Achieving EUCC certification demonstrates that your ICT product complies with rigorous cybersecurity standards, enhancing its credibility and marketability within the European market. It also facilitates easier access to multiple EU countries by eliminating the need for multiple national certifications.
What is the process for obtaining EUCC certification?
The EUCC certification process involves several key steps:
Application: Apply to a designated certification body accredited under the EUCC scheme.
Preparation: Hire consultants, review documentation through training, and perform an internal audit to ensure readiness for evaluation.
Evaluation: An independent assessment of your product's security features and documentation is conducted.
Certification: Upon successful evaluation, a certificate is issued, confirming compliance with EUCC standards.
Engaging with experienced certification bodies and IT Security Evaluation Facilities (ITSEFs) can streamline this process.
Related Articles


